When I initially deployed Sysmon earlier last year I was amazed by the amount of details it gathered as well as the huge amount of logs that my ELK stack was consuming. I decided to run it for a few weeks to get an idea of what was “normal” in my environment and later filter out those reoccurring events. If you really want to know what’s going on in your environment you should take this approach and filter as needed, it will take some time but you will feel confident that nothing is slipping through the cracks.
Since Sysmon doesn’t have advanced filtering (as of version 5.02), we will do a combination of Sysmon configuration filtering and Logstash configuration filtering to get exactly what we need.
Now that you’ve been collecting these logs for some time, let’s start filtering out items that are generating too many logs.
Here’s my logstash configuration (data being sent through Winlogbeat from my WEF server- Follow this guide to get this setup in your environment) or this for non-domain environment)
input {
beats {
port => 5000
}
}
#Sysmon Filtering
#1 Sysmon - remove Sha256= from field FileStream
filter {
if [log_name] == "Microsoft-Windows-Sysmon/Operational" and [event_id] == 15 {
mutate {
gsub => ["[event_data][Hash]", "SHA256=", ""]
}
}
}
#2 Sysmon - remove Sha256= from field Process Create (rule: ProcessCreate)
filter {
if [log_name] == "Microsoft-Windows-Sysmon/Operational" and [event_id] == 1 {
mutate {
gsub => ["[event_data][Hashes]", "SHA256=", ""]
}
}
}
#3 Drops Sysmon Events - NetworkConnect
filter {
if [log_name] == "Microsoft-Windows-Sysmon/Operational" and [task] == "Network connection detected (rule: NetworkConnect)"
and [event_data][Image] == "C:\Program Files (x86)\Dropbox\Client\Dropbox.exe"
or [event_data][Image] == "C:\Program Files (x86)\Mozilla Firefox\firefox.exe"
or [event_data][Image] == "C:\Program Files\Mozilla Firefox\firefox.exe"
or [event_data][Image] == "C:\Program Files (x86)\Adobe\Adobe Creative Cloud\CoreSync\CoreSync.exe"
#microsoft IPs
or [event_data][DestinationIp] == "64.4.54.254"
or [event_data][DestinationIp] == "64.4.54.253" {
drop { }
}
}
#4 Drops Sysmon Events - ProcessCreate
filter {
if [log_name] == "Microsoft-Windows-Sysmon/Operational" and [task] == "Process Create (rule: ProcessCreate)"
and [event_data][Image] == "C:\Windows\Microsoft.NET\Framework\v....\mscorsvw.exe"
or [event_data][Image] == "C:\Windows\Microsoft.NET\Framework64\v...\mscorsvw.exe"
or [event_data][CommandLine] == "C:\Windows\system32\Macromed\Flash\FlashPlayerUpdateService.exe" {
drop { }
}
}
output {
elasticsearch
{ hosts => ["http://elastic2ipaddress:9200","http://elastic3ipaddress.44:9200","http://elastic1ipaddress:9200"]
index => "logstash-winlogs"
}
}
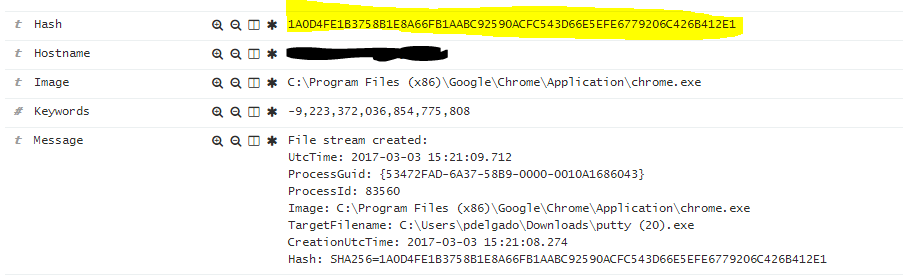
Filter #1 and #2 – Removes leading SHA256= from all file hashes generated by sysmon (See image below).
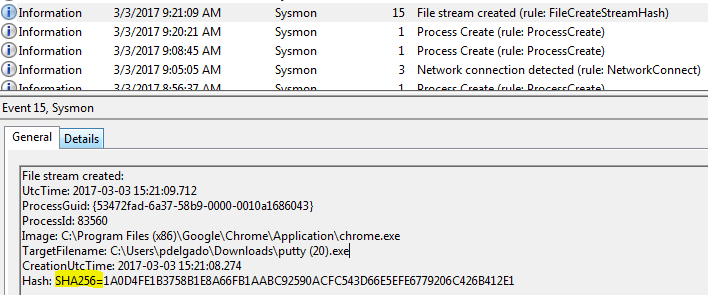
This will help you out whenever you are trying to integrate any type of file hash lookup intel to your data such as Virus total (See guide here).
This is how the data will be stored in Elasticsearch
Filter #3 – Drops expected network connections or applications that generate network connections.
The current filter would drop a log that would match this event based on
[event_data][Image] == “C:\Program Files\Mozilla Firefox\firefox.exe”
"event_data": {
"User": "NT AUTHORITY\\NETWORK SERVICE",
"Image": "C:\Program Files (x86)\Mozilla Firefox\firefox.exe",
"SourcePort": "49206",
"SourceHostname": "AQDV11",
"DestinationPort": "80",
"DestinationPortName": "http",
"UtcTime": "2017-03-04 05:30:57.409",
"DestinationIp": "216.58.218.174",
"Initiated": "true",
"SourceIp": "192.x.x.x",
"DestinationIsIpv6": "false",
"Protocol": "tcp"
As you can see, you may use any of the fields generated and create additional filters based on if statements.
Filter # 4 – Drops newly created processes.
This will probably be one of the most chatty logs; therefore, I would suggest to filter out these on your Sysmon configuration; however, for processes such as svchost.exe, csrss.exe, conhost.exe, services.exe,etc, I would go with Logstash and add additional logic (if statements for other fields such as ParentCommandLine, CommandLine, and User to filter out normal activity processes.
Here’s an example:
For process: sdclt.exe with a parent Image of C:\Windows\system32\services.exe and Command Line C:\Windows\System32\sdclt.exe /CONFIGNOTIFICATION
# Sysmon General sdclt.exe DROP
filter {
if [log_name] == "Microsoft-Windows-Sysmon/Operational" and [event_id] == 1
and [event_data][ParentImage] == "C:\Windows\system32\services.exe"
and [event_data][Image] == "C:\Windows\System32\sdclt.exe"
and [event_data][CommandLine] == "C:\Windows\System32\sdclt.exe /CONFIGNOTIFICATION" {
drop { }
}
}
Those are some examples of how you can filter out additional data being generated by Sysmon.
Lastly, here’s an example of a test Sysmon configuration that you may get started with.
<Sysmon schemaversion="3.2">
<!-- Capture SHA256 hashes -->
<HashAlgorithms>SHA256</HashAlgorithms>
<EventFiltering>
<!-- Logs All FileCreateStreamHash Events -->
<FileCreateStreamHash onmatch="exclude">
<TargetFilename condition="end with">.directory</TargetFilename>
<TargetFilename condition="end with">.sxx</TargetFilename>
<TargetFilename condition="end with">.partial</TargetFilename>
<TargetFilename condition="end with">.tmp</TargetFilename>
<TargetFilename condition="contains">C:\Windows\CSC\v2.0.6\namespace\</TargetFilename>
</FileCreateStreamHash>
<!-- FileCreate -->
<FileCreate onmatch="include">
<TargetFilename condition="end with">.exe</TargetFilename>
<TargetFilename condition="end with">.pdf</TargetFilename>
<TargetFilename condition="end with">.vbs</TargetFilename>
<TargetFilename condition="end with">.doc</TargetFilename>
<TargetFilename condition="end with">.hta</TargetFilename>
<TargetFilename condition="end with">.xls</TargetFilename>
</FileCreate>
<!-- Registry AutoStart, Services,Debuggers -->
<RegistryEvent onmatch="include">
<TargetObject condition="contains">Windows\CurrentVersion\Run</TargetObject>
<TargetObject condition="contains">Windows\CurrentVersion\Image File Execution Options</TargetObject>
<TargetObject condition="contains">CurrentControlSet\Services</TargetObject>
<TargetObject condition="contains">Microsoft\Windows NT\CurrentVersion\Winlogon</TargetObject>
<TargetObject condition="contains">Microsoft\Windows\CurrentVersion\Policies\Explorer</TargetObject>
<TargetObject condition="contains">Microsoft\Windows\CurrentVersion\RunOnce</TargetObject>
<TargetObject condition="contains">System\CurrentControlSet\Services\Tcpip\parameters</TargetObject>
</RegistryEvent>
<!-- Log CreateRemoteThread -->
<CreateRemoteThread onmatch="include">
<TargetImage condition="image">lsass.exe</TargetImage>
<TargetImage condition="image">winlogon.exe</TargetImage>
</CreateRemoteThread >
<!-- Contains Microsoft or Windows -->
<DriverLoad onmatch="exclude">
<Signature condition="contains">microsoft</Signature>
<Signature condition="contains">windows</Signature>
<Signature condition="contains">Intel</Signature>
</DriverLoad>
<!-- do not log process termination -->
<ProcessTerminate onmatch="include"/>
<!-- Internal IPs are too chatty so we're only focusing on external Adresses -->
<NetworkConnect onmatch="exclude">
<DestinationIp condition="contains">192.168.</DestinationIp>
<DestinationIp condition="begin with">10.</DestinationIp>
<Image condition="end with">iexplore.exe</Image>
<Image condition="end with">chrome.exe</Image>
<Image condition="end with">outlook.exe</Image>
<Image condition="end with">lynchtmlconv.exe</Image>
<Image condition="end with">lync.exe</Image>
</NetworkConnect>
<!-- Exclude File Create time for Chrome -->
<FileCreateTime onmatch="exclude">
<Image condition="end with">chrome.exe</Image>
<Image condition="end with">firefox.exe</Image>
<Image condition="end with">outlook.exe</Image>
<Image condition="end with">iexplore.exe</Image>
</FileCreateTime>
<!-- ProcessCreate -->
<ProcessCreate onmatch="exclude">
<IntegrityLevel>System</IntegrityLevel>
<!-- Google Chrome -->
<Image condition="Is">C:\Program Files (x86)\Google\Chrome\Application\chrome.exe</Image>
<ParentCommandLine condition="contains">C:\Windows\system32\svchost.exe -k netsvcs</ParentCommandLine>
<ParentCommandLine condition="contains">SharedSection=1024,20480,768</ParentCommandLine>
<ParentCommandLine condition="contains">C:\Windows\system32\SearchIndexer.exe /Embedding</ParentCommandLine>
</ProcessCreate>
<!-- RawAccessRead -->
<RawAccessRead onmatch="exclude">
<Image>C:\Windows\System32\wbem\WmiPrvSE.exe</Image>
<Image>C:\Windows\System32\svchost.exe</Image>
</RawAccessRead>
</EventFiltering>
</Sysmon>
If you have any questions feel free to send me a message on Twitter @Pablis2010 where I’ll answer quicker.